Cybersecurity in a remote connected world
Hi There! I’m happy that you find your way to one of the series of blogs about Cloud Security. In this blog I’m challenging you — as a decision maker to think in the broader spectrum of protection of your organization.
As an IT-Pro I’m in daily meetings and conference calls to pitch solutions to protect organizations better.
From my opinion the security challenges of today are sometimes complex to explain. Definitely if we are still talking about IT of the last decade. Segmented teams, segmented responsibilities, no security ambition.. not a straight-forward vision like for example some customers are saying: “we see Cloud services as Microsoft 365 as a single-service” OR “It’s not the core of our organization” Therefore this article. I hope it brings value and understanding.
I’m a strong believer of consolidation and simplifying your IT-landscape to make it; Fast(er) for your business, budget efficient and realistic to maintain, understand and improve. If you don’t believe in these 3 core ambitions. I would be grateful to receive a reaction below to improve this arcticle. Now, let’s start.
You are a Microsoft-first organization
Believe it or not. Microsoft is gigantic.. Microsoft is a different company when Steve Balmer quit CEO and Satya Nadella has taken over the steering wheel. With ambition to empower each and every person to achieve more, Microsoft has embraced real change in the world.
Ambitions that were not focused on the big numbers and segmented solutions. Satya brought vision to connect all people and solutions into one Cloud-connected world. Not driven by their own agenda but integrated with their competitors, integrators, partners like it should be. To really help (their) customers –and because organizations don’t use Microsoft technology alone, it is a great success.
Think about Microsoft as a platform: Microsoft is levering 2 main solutions. A platform where you can collaborate; Microsoft 365 and a platform that can bring almost any system online; Microsoft Azure. — I will go into the platforms later in this article.
You are a Microsoft-first organization: If you are running Windows machines, using Exchange online for e-mail, SharePoint, Teams or OneDrive for collaboration you are a Microsoft-first organization. What I mean by that? -> If you’re still not talking about “put all eggs in the basket” your not seeing it straight. The Microsoft-first choice already has been made. You are just not using all features, yet.
Why Microsoft 365 for collaboration
There are mainly 3 big collaboration solutions. Microsoft 365, Google Workspace or Slack. They all are the same, in general if we talk about the purpose or problem they fix. They are a place to connect, collaborate, chat, meet, share data.
The most important part of “Why Microsoft 365” is the integration into one single platform. IF you would use Microsoft 365, all your company data is integrated in one single system. Easier to protect and all alerts in one place.
When we think about company data I’m sure that there are two places where almost all important data is located. On your servers, applications and company systems (Datacenter) and in Microsoft 365. How much data is already in Microsoft 365 today? 80%?
Microsoft Azure for your datacenter
Microsoft Azure for datacenter(s) — I’m sure you hate this title. Azure is no place to host traditional servers. Still I’m pitching; why not? Is it worse than your private-datacenter, distributed datacenter or cloud-datacenter?
Azure can help you as an organization to bring everything in the Microsoft Platform. Why? To have everything consolidated and close to each-other to measure the Security-maturity.
Azure can leverage solutions as-a-service which is far more better than infrastructure as-a-service but still powerful when it comes to single platform focus and security insights.
No Microsoft solutions for your Yes-Microsoft Security?
Do you feel the story getting build up? You have 80% of your documents and realtime communication in Microsoft 365. Your Microsoft servers are running somewhere — could be Azure (theoretically) so why should you still put no-cloud focus solutions and complex security solution in between? Than cannot even measure, control or react on alerts in your mainly used collaboration, services and server solutions?
Think with me; Almost all essentials business critical solutions are hosted in Microsoft 365 and Azure — but still you are thinking not to use Microsoft solutions for protection? Why?
My opinion: Microsoft hasn’t had the best reputation when it comes to secure-systems — before. But things has changed and due the fact of these billion dollar investment, acquisitions, Microsoft Cloud native and Cloud focused solutions you can leverage so much that you just can’t with your on-premise focused solutions.
And by the way; if you’re still using on-premise focused solutions. Can they protect the Cloud? The place where we put 80% of all our corporate data and infrastructure?
Remote working trends are here to stay
“Employees want the best of both worlds: over 70 percent of workers want flexible remote work options to continue, while over 65 percent are craving more in-person time with their teams. To prepare, 66 percent of business decision makers are considering redesigning physical spaces to better accommodate hybrid work environments. The data is clear: extreme flexibility and hybrid work will define the post-pandemic workplace.”
Source: The Next Great Disruption Is Hybrid Work—Are We Ready? (microsoft.com)
It brings us the the point of vision. We know that the datacenter as it is, is not needed anymore in the same architecture as in the good old days. Why not treat it as a; connect from anywhere solution? What is your response, your vision to empower your workers to collaborate and thrive in your business?
Zero Trust: A new concept of layered approach which kills the fish tank within corporate infrastructure

Corporate datacenter with all servers running in a virtualized state, segmented with additional security solutions. Segmentation on networking storage and many more services. It’s so extreme complex. One mistake could impact everything — and we still love it.. (no business driver here, don’t you think?)
Next to mistakes: Ransomware, targeted-attacks, phishing attacks,.. and all other bad-actors took this opportunity to infiltrate and bring this infrastructure down. Sell data. Bottom-line: it became so complex to react on all aspect of just only the core infrastructure where your servers and services are.
Microsoft didn’t invented the layered approach when it comes to: Identity, Devices, Services, Data and Network. It’s no new model nor real solution that fixes any problem. No, it’s a way of understanding and integration of your assets to bring them in a layered solution where it cannot touch the asset next to it. And isolation was always the biggest problem of own infrastructure. Even when your organization is huge it’s still extremely hard to take everything under control and secured. The right conclusion: Layered approach.
If you want to read more why and how see this article: how to build a Zero Trust Modern Workplace with Microsoft 365
How Microsoft is helping with solutions to protect your business?
When you dare to choose Microsoft as your primary Security platform more automation and integration can be achieved. I’ve created some basic examples that are hard to do but now are easily activated. Read more examples in this article.
Example 1: Identity protection: Require Password Change when the risk is high. Create process that describes the action required as: Call user – validate risk – validate credentials (real person) ..
These examples are in the core of the workplace. These tasks are killing IT-teams with unlimited effort without focusing on real import improvements.

Microsoft Defender for Endpoints is not an antivirus solution. It’s a global solution where you can see every alert, software patch, inventory, asset-management but also the real risk in the workplace. Microsoft Defender for Endpoint is an enterprise endpoint security platform designed to help you to: prevent, detect, investigate, and respond to advanced threats.
Microsoft Defender for Endpoints also captures alerts through the workplace and gives pragmatic alerts and advices with top-recommendations.
Microsoft Defender for Identity is delivering Active-directory alerts to for example Cloud App Security, so you can automate and fix risks.
Defender for Office 365 is protecting your e-mail system.
Azure AD Identity Protection is protecting your most important identities in the Cloud. As you could see in the example of the user-risk.
Cloud App Security is able to mitigate risks — it can be a broker between the endpoint and the internet. OR it could tell you who’s working with non-trusted platforms or applications.
Protect everything with Microsoft in the Cloud
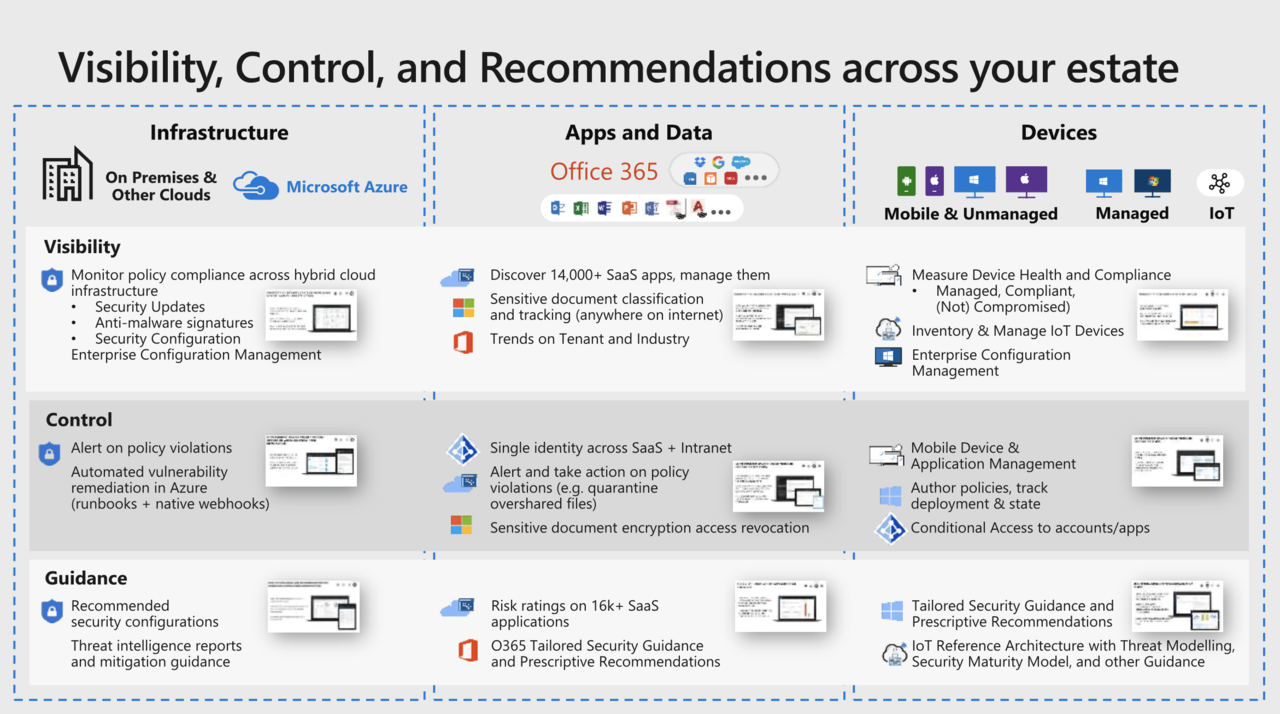
If you are able to protect; infrastructure, applications, data, identities and devices you have won a huge security maturity. By only using only Microsoft technology — isn’t it great?

How to achieve a realistic security roadmap
- Define what is important as key drivers for your business. Go-fast, go pragmatic,..
- Write down the core collaboration systems and what is in place to protect, now. Write down the collaterals — which are hard to protect.
- Define the infrastructure and application ambition over the next +5 years. What will change? What cannot change? What is there to protect? Start with creating an high-level overview of all services core to the organization. See how you want to protect them.
- Decide on the platform. Choose long-term. Embed the core into one platform.
- Create procedure for your Security Operation or Automate. (read this!)
- Budget Integrate in the broader IT-landscape + collaboration stack.
- Start.
Still questions after reading this blog — please give some feedback in the comment section. Thank you so much for reading! If you want to talk reach out on Linkedin or Twitter.